I was going through, developers.facebook.com and found that it allows itself to be iframed. It includes all the documentation and examples for using the Facebook Graph API and other products like the Legacy REST API, FQL, Chat API. An attacker can do a whole lot of stuff with this once he iframes this.
I decided to write on one of the attacks that is possible with this bug. As we all know, the documentation includes some excellent examples for using the API with some nifty access tokens with the credentials of the currently logged in user. This special token in the documentation comes with some extra special rights like read_stream, user_status, user_birthday, user_relationships and much more rights which even your normal friends can’t see.
Stealing the access token
Now the exciting part is to get the token sitting inside the source code. It’s possible to steal this with many attack vectors, and I decided to write a PoC using a Double drag and drop technique which works on Firefox and IE. Google chrome can resist this attack because it disallows Cross-Domain drag & drops and also view-source can’t be iframed on Chrome.
Double drag & drop
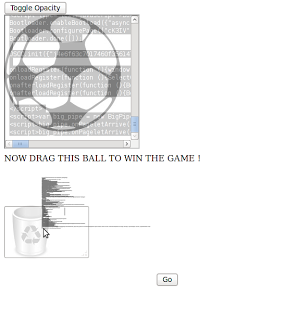
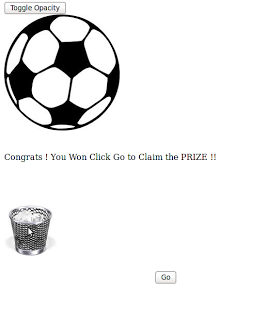
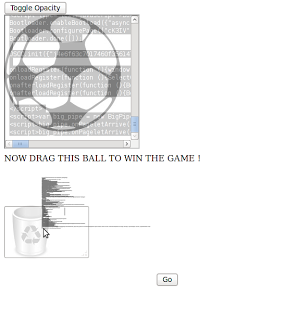
Here is a proof of concept which uses view-source to iframe the source code of the page containing the access token. It’s better to use a double view-source to make everything as a text and disable all clickable links. The trick is to fool the user, by making him play a game with a ball and a trash can. I’ll show some screenshots of what a real attack would look like. A video would have been better, but am just lazy now.
1. The attacker asks the user to drag the ball into the basket.
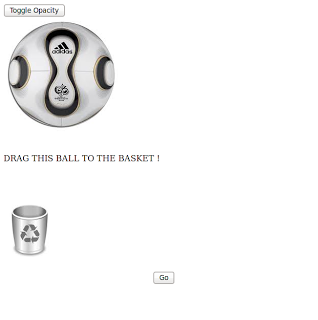
2. The attacker creates another ball and asks the user to repeat.

3. The attacker asks the user to click Go to Win the game.
What happened?
Here is what happened behind the scenes!
1. First drag, everything in the iframe gets Selected
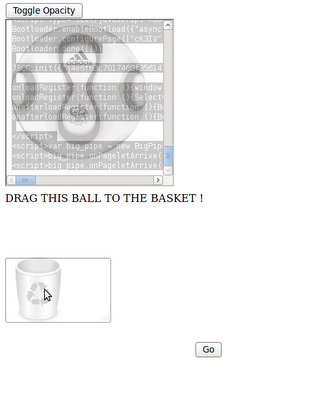
2. Second drag , the mighty cross-domain drag
The user clicks go and the source of the page is sent to the attacker